Press Information
MHI and NTT Group Begin Sales of "InteRSePT®" Cyber Security Technology Providing Safe and Secure Operation of Control Systems
-- Advanced Security at All Operating States with Low Cost and Space Savings --
-- Advanced Security at All Operating States with Low Cost and Space Savings --
Tokyo, April 25, 2018 - Mitsubishi Heavy Industries, Ltd. (MHI), Nippon Telegraph and Telephone Corporation (NTT), NTT DATA Corporation (NTT DATA), and NTT Communications Corporation (NTT Com) have commercialized "InteRSePT®"*1, a jointly developed cyber security technology for critical infrastructure control systems. InteRSePTInteRSePT® provides real-time anomaly detection and response for unknown cyber-attacks, contributing to safe and secure system operations. Sales of the system will begin in May. MHI and NTT are actively developing markets for the technology in commercial fields where continuous availability*2 is critical, such as thermal power generation facilities and chemical plants.
1. Background to the Development
In addition to the existing security countermeasures, such as IDS / IPS*3 and firewalls*4 to prevent cyber-attacks from malware*5 and DDoS*6, in recent years measures have become necessary to counter advanced cyber-attacks that monitor the operating characteristics and control commands of the target device, and change the timing of network communication or contents of commands to cause the target device to fail.
MHI and NTT, in response to growing needs, began research and development on security technologies in March 2016. The InteRSePT® prototype was completed in November that year, combining the highly reliable and safe control technologies developed by MHI for the fields of defense and space, with security control technology*7 developed by NTT.
Evaluation of the prototype and conformance testing for control systems was then conducted at Cyber Lab, MHI's facility in Tokyo for security development and testing. The functionality of InteRSePT® was further improved and the range of applications broadened to include the operations and maintenance (O&M) businesses. This led to commercialization and the launch of sales.
2. Features of InteRSePT®
InteRSePT® comprises a real-time network monitoring system (RNMS) and a security management system (SMS). The system monitors sensor information and other data flows in networks in an integrated manner, and detects cyber-attacks that exploit control commands, which are difficult to detect and respond to with conventional technology. By changing the security remediation rules on each operating state of the target device, the system provides early detection of anomalies, and allows for a rapid response to even unknown cyber-attacks while maintaining availability. (Joint patent pending)
InteRSePT® is able to provide detailed confirmation of control system networks, and offers exceptional compatibility with a wide range of industrial facilities and devices.
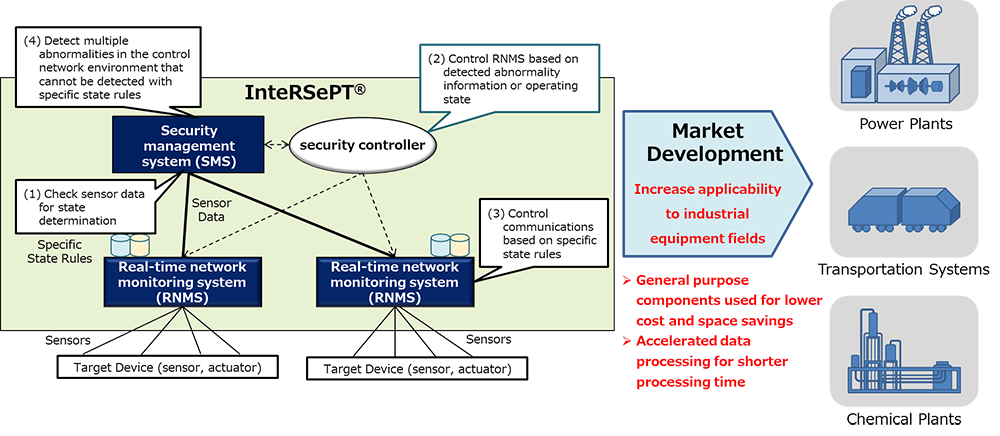
InteRSePT®conceptual diagram
- (1) The system collects and analyzes packets of sensor information flows in the control system network to determine the operating state.
- (2) The communication control rules of the RNMS are changed according to the actual operating state and other factors.
- (3) Packets are analyzed, and blocked or passed based on the rules.
- (4) Multiple sensor information is aggregated in the SMS, and the behavior of the entire control system monitored in an integrated manner to allow for early detection (behavior detection processing*8), and a rapid response to even unknown cyber-attacks.
3. Productization
For the productization, RNMS utilizing commercial-off-the-shelf hardware and integrated with network switch provides low cost, space savings and easier system installability. In addition, the SMS improved its behavior detection processing speed by adopting distributed processing.
4. Role of each company
| MHI | Sales of InteRSePT® Development of data analysis, operational status estimates, and anomaly detection methods according to the control system, as well as handling and recovery methods, and design optimization |
|---|---|
| NTT | Provide security control technology and RNMS developed by the NTT, |
| NTT DATA | Support market development for security solutions based on the InteRSePT® system developed by MHI and the NTT Group |
| NTT Com | Development of technologies related to data accumulation and anomaly detection necessary for market application of the NTT's core technologies, and productization of security solutions |
5. Future plans
Going forward, MHI NTT, NTT DATA, and NTT Com will cooperate to promote InteRSePT®'s low cost, advanced functionality, fast processing capabilities, and easy installability to a wide range of industries, as well as propose individual security solutions, and develop markets.
Further, we will effectively utilize the aggregated and analyzed sensor data from InteRSePT® to not only security countermeasures but also operational parameters optimization and preventive maintenance to reduce time required for maintenance. We will develop an O&M total solutions business to help enhance operational efficiency for customers.
Notes
*1 InteRSePT®: Abbreviation of Integrated Resilient Security and Proactive Technology - a registered trademark of MHI, in Japan
*2 Availability: Continuous operation of a system without stoppage
*3 IDS / IPS: Intrusion Detection System / Intrusion Protection System-systems to detect and protect against cyber intrusions
*4 Firewall: System for discrimination and reporting of unauthorized access
*5 Malware: Abbreviation of malicious software
*6 DDoS: Distributed Denial of Service attack
*7 Security control technology: Technologies that collect and analyze cyber-attack related information including target device / system status and anomaly events, and comprehensively control diversified security appliances
*8 Behavior detection processing: Detection of behaviors in a device or system different from its normal operating status
About MHI Group
Mitsubishi Heavy Industries (MHI) Group is one of the world’s leading industrial groups, spanning energy, smart infrastructure, industrial machinery, aerospace and defense. MHI Group combines cutting-edge technology with deep experience to deliver innovative, integrated solutions that help to realize a carbon neutral world, improve the quality of life and ensure a safer world. For more information, please visit www.mhi.com or follow our insights and stories on spectra.mhi.com.






